linux中防火墙策略管理工具iptables
内容导读
互联网集市收集整理的这篇技术教程文章主要介绍了linux中防火墙策略管理工具iptables,小编现在分享给大家,供广大互联网技能从业者学习和参考。文章包含31430字,纯文字阅读大概需要45分钟。
内容图文
防火墙:内网和外网之间过滤流量的服务

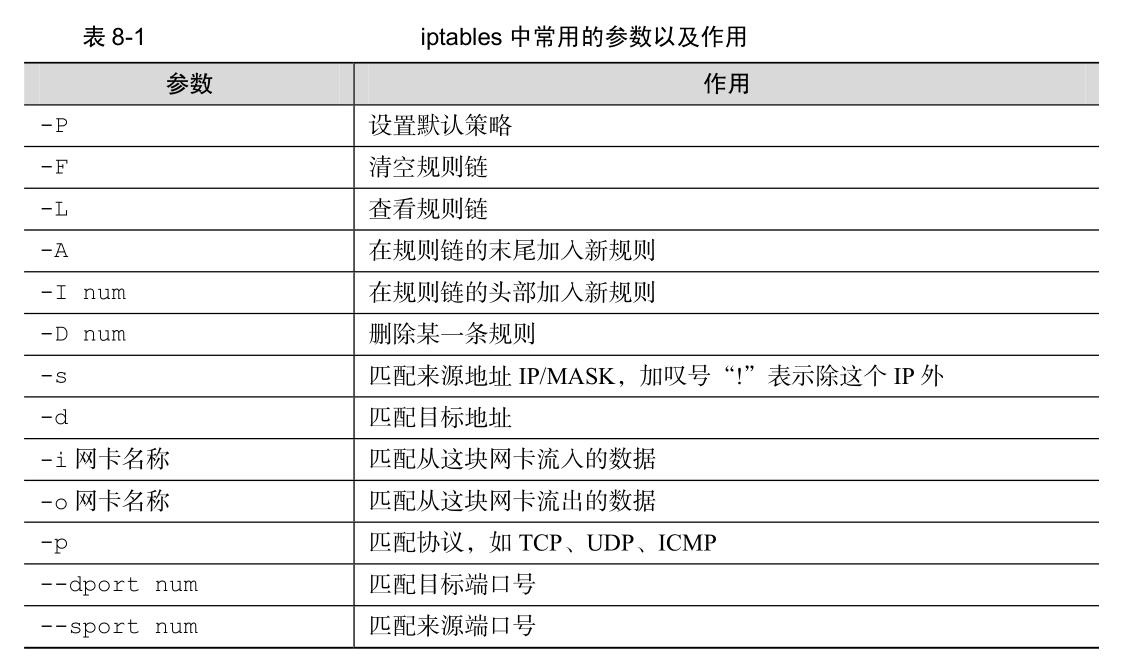
1、iptables常用的命令参数
2、查看已有的防火墙规则链
[root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination ACCEPT all -- anywhere anywhere ctstate RELATED,ESTABLISHED ACCEPT all -- anywhere anywhere INPUT_direct all -- anywhere anywhere INPUT_ZONES_SOURCE all -- anywhere anywhere INPUT_ZONES all -- anywhere anywhere ACCEPT icmp -- anywhere anywhere REJECT all -- anywhere anywhere reject-with icmp-host-prohibited Chain FORWARD (policy ACCEPT) target prot opt source destination ACCEPT all -- anywhere anywhere ctstate RELATED,ESTABLISHED ACCEPT all -- anywhere anywhere FORWARD_direct all -- anywhere anywhere FORWARD_IN_ZONES_SOURCE all -- anywhere anywhere FORWARD_IN_ZONES all -- anywhere anywhere FORWARD_OUT_ZONES_SOURCE all -- anywhere anywhere FORWARD_OUT_ZONES all -- anywhere anywhere ACCEPT icmp -- anywhere anywhere REJECT all -- anywhere anywhere reject-with icmp-host-prohibited Chain OUTPUT (policy ACCEPT) target prot opt source destination OUTPUT_direct all -- anywhere anywhere Chain FORWARD_IN_ZONES (1 references) target prot opt source destination FWDI_public all -- anywhere anywhere [goto] FWDI_public all -- anywhere anywhere [goto] Chain FORWARD_IN_ZONES_SOURCE (1 references) target prot opt source destination Chain FORWARD_OUT_ZONES (1 references) target prot opt source destination FWDO_public all -- anywhere anywhere [goto] FWDO_public all -- anywhere anywhere [goto] Chain FORWARD_OUT_ZONES_SOURCE (1 references) target prot opt source destination Chain FORWARD_direct (1 references) target prot opt source destination Chain FWDI_public (2 references) target prot opt source destination FWDI_public_log all -- anywhere anywhere FWDI_public_deny all -- anywhere anywhere FWDI_public_allow all -- anywhere anywhere Chain FWDI_public_allow (1 references) target prot opt source destination Chain FWDI_public_deny (1 references) target prot opt source destination Chain FWDI_public_log (1 references) target prot opt source destination Chain FWDO_public (2 references) target prot opt source destination FWDO_public_log all -- anywhere anywhere FWDO_public_deny all -- anywhere anywhere FWDO_public_allow all -- anywhere anywhere Chain FWDO_public_allow (1 references) target prot opt source destination Chain FWDO_public_deny (1 references) target prot opt source destination Chain FWDO_public_log (1 references) target prot opt source destination Chain INPUT_ZONES (1 references) target prot opt source destination IN_public all -- anywhere anywhere [goto] IN_public all -- anywhere anywhere [goto] Chain INPUT_ZONES_SOURCE (1 references) target prot opt source destination Chain INPUT_direct (1 references) target prot opt source destination Chain IN_public (2 references) target prot opt source destination IN_public_log all -- anywhere anywhere IN_public_deny all -- anywhere anywhere IN_public_allow all -- anywhere anywhere Chain IN_public_allow (1 references) target prot opt source destination ACCEPT tcp -- anywhere anywhere tcp dpt:ssh ctstate NEW Chain IN_public_deny (1 references) target prot opt source destination Chain IN_public_log (1 references) target prot opt source destination Chain OUTPUT_direct (1 references) target prot opt source destination
3、清空已有的防火墙策略规则链
[root@PC1 ~]# iptables -F [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
4、将INPUT规则链设置为拒绝
[root@PC1 ~]# iptables -L | head Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) [root@PC1 ~]# iptables -P INPUT DROP ## (防火墙默认的拒绝动作只能是DROP,而不能填写REJECT) [root@PC1 ~]# iptables -L | head Chain INPUT (policy DROP) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references)
5、向INPUT规则链中添加允许ICMP流量的策略规则
[root@PC1 ~]# ifconfig | head -n 3
eno16777728: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.10.10 netmask 255.255.255.0 broadcast 192.168.10.255
inet6 fe80::20c:29ff:fe66:37f7 prefixlen 64 scopeid 0x20<link>
[root@PC1 ~]# ping -c 3 192.168.10.10
PING 192.168.10.10 (192.168.10.10) 56(84) bytes of data.
--- 192.168.10.10 ping statistics ---
3 packets transmitted, 0 received, 100% packet loss, time 1999ms
## 以上部分为测试,ping命令的服务属于icmp,当前不能执行ping命令,说明没有开通icmp流量
[root@PC1 ~]# iptables -L ## 列出当前的规则链 Chain INPUT (policy DROP) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
[root@PC1 ~]# iptables -I INPUT -p icmp -j ACCEPT ## 设置允许icmp流量
[root@PC1 ~]# ping -c 3 192.168.10.10 PING 192.168.10.10 (192.168.10.10) 56(84) bytes of data. 64 bytes from 192.168.10.10: icmp_seq=1 ttl=64 time=0.031 ms 64 bytes from 192.168.10.10: icmp_seq=2 ttl=64 time=0.033 ms 64 bytes from 192.168.10.10: icmp_seq=3 ttl=64 time=0.043 ms --- 192.168.10.10 ping statistics --- 3 packets transmitted, 3 received, 0% packet loss, time 1999ms rtt min/avg/max/mdev = 0.031/0.035/0.043/0.008 ms
[root@PC1 ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination ACCEPT icmp -- anywhere anywhere Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
6、删除icmp流量的允许策略
[root@PC1 ~]# iptables -D INPUT 1 [root@PC1 ~]# ping -c 3 192.168.10.10 PING 192.168.10.10 (192.168.10.10) 56(84) bytes of data. --- 192.168.10.10 ping statistics --- 3 packets transmitted, 0 received, 100% packet loss, time 2000ms [root@PC1 ~]# iptables -L Chain INPUT (policy DROP) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
7、将默认的允许规则设置为允许
[root@PC1 ~]# iptables -P INPUT ACCEPT [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
8、将INPUT规则链设置为只允许指定网段的主机访问本机的22端口,拒绝其他所有主机的流量
[root@PC1 ~]# iptables -I INPUT -s 192.168.20.0/24 -p tcp --dport 22 -j ACCEPT [root@PC1 ~]# iptables -A INPUT -p tcp --dport 22 -j REJECT [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination ACCEPT tcp -- 192.168.20.0/24 anywhere tcp dpt:ssh REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
[root@PC2 ~]# ifconfig | head -n 3
eno16777728: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.10.20 netmask 255.255.255.0 broadcast 192.168.10.255
inet6 fe80::20c:29ff:fe25:bb3e prefixlen 64 scopeid 0x20<link>
[root@PC2 ~]# ssh 192.168.10.10
ssh: connect to host 192.168.10.10 port 22: Connection refused
9、向INPUT规则链中添加拒绝所有人访问本机12345端口的策略规则
[root@PC1 ~]# iptables -I INPUT -p tcp --dport 12345 -j REJECT [root@PC1 ~]# iptables -I INPUT -p udp --dport 12345 -j REJECT [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable ACCEPT tcp -- 192.168.20.0/24 anywhere tcp dpt:ssh REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
10、向INPUT规则链中添加拒绝192.168.10.5主机访问本机80端口(web服务)的策略规则
[root@PC1 ~]# iptables -I INPUT -p tcp -s 192.168.10.5 --dport 80 -j REJECT [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination REJECT tcp -- 192.168.10.5 anywhere tcp dpt:http reject-with icmp-port-unreachable REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable ACCEPT tcp -- 192.168.20.0/24 anywhere tcp dpt:ssh REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
11、向INPUT规则链中添加拒绝所有主机访问本机1000~1024端口的策略规则
[root@PC1 ~]# iptables -I INPUT -p tcp --dport 1000:1024 -j REJECT [root@PC1 ~]# iptables -I INPUT -p udp --dport 1000:1024 -j REJECT [root@PC1 ~]# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination REJECT udp -- anywhere anywhere udp dpts:cadlock2:1024 reject-with icmp-port-unreachable REJECT tcp -- anywhere anywhere tcp dpts:cadlock2:1024 reject-with icmp-port-unreachable REJECT tcp -- 192.168.10.5 anywhere tcp dpt:http reject-with icmp-port-unreachable REJECT udp -- anywhere anywhere udp dpt:italk reject-with icmp-port-unreachable REJECT tcp -- anywhere anywhere tcp dpt:italk reject-with icmp-port-unreachable ACCEPT tcp -- 192.168.20.0/24 anywhere tcp dpt:ssh REJECT tcp -- anywhere anywhere tcp dpt:ssh reject-with icmp-port-unreachable Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain FORWARD_IN_ZONES (0 references) target prot opt source destination Chain FORWARD_IN_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES (0 references) target prot opt source destination Chain FORWARD_OUT_ZONES_SOURCE (0 references) target prot opt source destination Chain FORWARD_direct (0 references) target prot opt source destination Chain FWDI_public (0 references) target prot opt source destination Chain FWDI_public_allow (0 references) target prot opt source destination Chain FWDI_public_deny (0 references) target prot opt source destination Chain FWDI_public_log (0 references) target prot opt source destination Chain FWDO_public (0 references) target prot opt source destination Chain FWDO_public_allow (0 references) target prot opt source destination Chain FWDO_public_deny (0 references) target prot opt source destination Chain FWDO_public_log (0 references) target prot opt source destination Chain INPUT_ZONES (0 references) target prot opt source destination Chain INPUT_ZONES_SOURCE (0 references) target prot opt source destination Chain INPUT_direct (0 references) target prot opt source destination Chain IN_public (0 references) target prot opt source destination Chain IN_public_allow (0 references) target prot opt source destination Chain IN_public_deny (0 references) target prot opt source destination Chain IN_public_log (0 references) target prot opt source destination Chain OUTPUT_direct (0 references) target prot opt source destination
12、保存所有的设置,使其开机后依然生效
[root@PC1 ~]# service iptables save iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ]
内容总结
以上是互联网集市为您收集整理的linux中防火墙策略管理工具iptables全部内容,希望文章能够帮你解决linux中防火墙策略管理工具iptables所遇到的程序开发问题。 如果觉得互联网集市技术教程内容还不错,欢迎将互联网集市网站推荐给程序员好友。
内容备注
版权声明:本文内容由互联网用户自发贡献,该文观点与技术仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌侵权/违法违规的内容, 请发送邮件至 gblab@vip.qq.com 举报,一经查实,本站将立刻删除。
内容手机端
扫描二维码推送至手机访问。